You fill in the form. We customize every document. You deploy.
Choose any Ridgeline product and we customize it to your organization — your industry, your regulations, your technology stack, your risk profile. You complete one intake form. We deliver customized, ready-to-deploy documents in 7–10 business days. Fixed price. You own everything.
What this service is — and what it is not
What it is
Document customization. We take a Ridgeline product and rewrite it to reference your industry, your regulatory obligations, your technology stack, and your operational reality. You receive documents that are ready for your team to review and deploy.
What it is not
Not consulting. We do not advise on security strategy, conduct assessments, perform audits, recommend tools, implement controls, or manage your security program. We customize the documents. What you do with them is your decision.
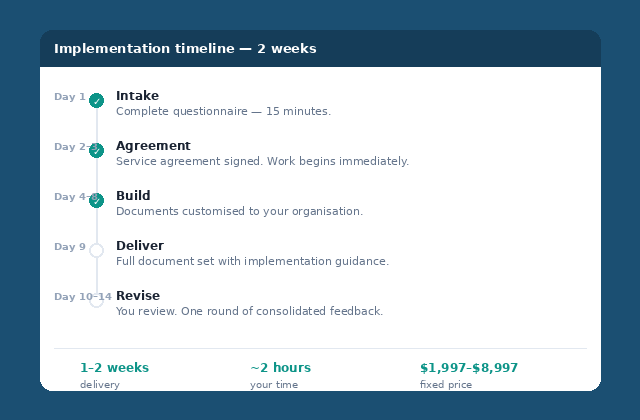
How It Works
Five steps. One form. Done.
Purchase
Choose a Ridgeline product and a customization tier. Product and service can be purchased together or separately.
Intake
Complete the online intake form — company details, named individuals, industry, tech stack, regulatory obligations, team size, approval chains, internal system names, target framework. 30–45 minutes. One form captures everything.
Customize
We apply every customization action in your tier — industry context, regulatory mapping, control applicability, risk pre-population, parameter calibration, and more. Your documents reference your organization, not a generic template.
Review
You receive your customized documents as editable files. Review at your pace. Return revision notes within 10 business days.
Final Delivery
We deliver the final revision within 5 business days of receiving your notes. Deploy to your organization.
What We Customize
7 actions applied to your documents
Every tier includes some or all of these actions. This is what separates a customized document from a template with your name on it.
Industry Context
Generic language rewritten to reference your industry, sector terminology, and operating environment.
Before: "The organization shall protect sensitive data in accordance with applicable regulations."
After: "As a healthcare services provider processing protected health information (PHI), [Company] shall protect patient data in accordance with HIPAA Security Rule (45 CFR Part 164), state breach notification laws applicable to operations in Texas and California, and contractual obligations under active Business Associate Agreements."
Regulatory Mapping
We identify which regulations apply based on your industry, geography, data types, and customer base. Inapplicable controls marked N/A with rationale. Overlooked obligations flagged.
Example: 200-person US SaaS company processing EU customer payment data → GDPR, PCI-DSS 4.0, SOC 2, CCPA, state breach notification laws. Physical manufacturing controls, classified data controls, healthcare requirements → marked N/A.
Control Applicability
Each control adjusted for your environment. Marked applicable, partially applicable (with explanation), or not applicable (with rationale).
Example: Cloud-first SaaS company → physical server room controls marked N/A, backup controls rewritten for SaaS shared responsibility model, network segmentation rewritten for cloud-native architectures.
Risk Pre-Population
Generic risks replaced with industry-specific, environment-relevant risks. Calibrated likelihood and impact ratings with rationale based on current threat intelligence.
Before: "Unauthorized access to information systems — Likelihood: Medium, Impact: High"
After: "Compromise of customer payment records via AiTM phishing targeting finance staff, exploiting password-only authentication on payment portal — Likelihood: High (financial sector targeted in 67% of credential phishing campaigns, 2024-2025), Impact: Critical (PCI-DSS breach notification, card brand fines, $150-$400 per record)"
Parameter Calibration
Timelines, thresholds, frequencies, and retention periods set to realistic values for your size, capacity, and regulatory requirements. These numbers are where most policies fail audits.
Patch timelines · Access review frequency · Risk assessment cadence · Data retention periods · Incident response deadlines · Authentication requirements · Backup RPO/RTO · Training frequency · Vulnerability scan schedules — all calibrated to what your organization can actually sustain.
Technology Stack References
COMPLIANCE TIERGeneric technology categories replaced with your actual platform names and configurations.
Before: "The organization shall deploy endpoint protection on all managed devices."
After: "Microsoft Defender for Endpoint shall be deployed to all domain-joined Windows and macOS devices managed via Microsoft Intune. Tamper protection enabled. Cloud-delivered protection configured with automatic sample submission."
Framework Cross-Referencing
COMPLIANCE TIEREvery control mapped to your target framework(s). Your auditor sees the mapping without building it.
Example: Access control standard → ISO 27001:2022 A.8.3, SOC 2 CC6.1, NIST CSF 2.0 PR.AA-01, CIS v8 Control 6
Pricing
Two tiers. Clear scope. Fixed price.
Foundation Customization
$1,997
+ product purchase (separate)
Scope
One Ridgeline product — any toolkit or suite.
Actions included
✓ Industry context
✓ Regulatory mapping
✓ Control applicability
✓ 15 pre-populated risks
✓ Parameter calibration
— Technology stack references
— Framework cross-referencing
Intake: 30-minute form
Timeline: 7 business days
Revisions: 1 round
Purchase → or start with the intake form →Compliance Customization
$3,497
+ product purchase (separate)
Scope
One Ridgeline product + target framework alignment.
Actions included
✓ Industry context
✓ Regulatory mapping
✓ Control applicability
✓ 20 pre-populated risks
✓ Parameter calibration
✓ Technology stack references
✓ Framework cross-referencing
Intake: 45-minute form + tech questionnaire
Timeline: 10 business days
Revisions: 1 round
Purchase → or start with the intake form →Four approaches to the same outcome
Scope boundaries
To avoid misunderstanding, the following are explicitly outside the scope of all customization tiers.
Security advice or recommendations. We customize documents to reflect your stated environment. We do not advise on what your security strategy should be.
Tool selection or configuration. We reference the tools you tell us you use. We do not recommend tools or configure them.
Audit preparation or representation. We customize documents for your target framework. We do not prepare you for audit, attend audits, or represent your organization.
Risk assessment. We pre-populate risks based on your industry and environment. We do not conduct a formal risk assessment of your organization.
Gap analysis. We do not assess your current security posture or identify gaps between your current state and your target framework.
Implementation. We do not deploy policies, configure systems, train staff, or manage any aspect of putting documents into operational use.
Ongoing maintenance. Customization is a one-time engagement. Future updates can be purchased as a new engagement.
What changes for your organization
Before
- Security questionnaires take days and the answers are vague
- No documented policies — informal practices only
- Audit readiness is a guess, not a measurement
- Board asks about security posture — you have no data
- Customer due diligence is a scramble every time
After
- Security questionnaires answered same-day from documented evidence
- Professional documentation customized to your organization
- Audit-ready documentation structured to your target framework
- Evidence-based reporting for board and stakeholders
- Insurance renewals backed by documented controls
Quality You Can Verify
See what you're getting before you commit
Download free samples from our public resource library. The documents we customize for you follow the same structure, depth, and professional standard — tailored to your organization.
Common questions
How is this different from hiring a consultant?
Consultants build documentation from scratch — which is why it takes months and costs $25K+. We start with proven, refined documentation and customize it to your organization. Same professional standard, fraction of the time and cost. And you keep the editable source files.
Can any product be customized?
Any live product in the catalog. The customization tier determines the depth — Foundation covers industry context, regulatory mapping, control applicability, risks, and parameters. Compliance adds technology-specific language and framework cross-referencing.
Do I need to buy the product separately?
Yes. The product and customization service are separate purchases. You can buy them together or purchase customization for a product you already own.
How much of my time does this require?
30–45 minutes to complete the intake form. That is the only input we need. You then review the delivered documents at your pace and return any revision notes within 10 business days. No calls, no workshops, no ongoing meetings.
What is the difference between Foundation and Compliance?
Foundation (Actions 1-5) customizes content, risks, and parameters to your organization but uses generic technology references and the product's default framework mapping. Compliance (Actions 1-7) adds your specific technology platforms by name and cross-references every control to your target audit framework. If you are preparing for a specific audit, choose Compliance.
Can you guarantee we will pass the audit?
No — and anyone who guarantees certification is misleading you. We deliver documentation customized to your target framework's requirements. Whether you pass depends on implementing the controls, not just documenting them.
What if I need multiple products customized?
Purchase multiple engagements — one per product. Each has its own intake, timeline, and delivery. Contact us if you have a larger scope to discuss.
What frameworks do you cover?
ISO 27001:2022, ISO 22301:2019, ISO 31000:2018, NIST CSF 2.0, NIST SP 800-171, CIS Controls v8, SOC 2 (Trust Services Criteria), CMMC 2.0, PCI-DSS 4.0, GDPR, DORA, CCPA, NIST AI RMF 1.0, and OWASP Top 10 for LLM Applications 2025.
What is your payment structure?
Payment in full before work begins. Fixed price for a defined deliverable — no hourly billing, no scope creep. Invoiced via Stripe — card or bank transfer.
What happens after delivery?
You own everything. Editable Word and Excel files. Review, revise (one round included), and deploy. Ongoing maintenance is your responsibility — future updates can be purchased as a new engagement.
Need your team to operate the program?
Our training platform at training.ridgelinecyber.com develops the skills to maintain the documentation we deliver — incident response, identity security, GRC, detection engineering, and more. 9 courses built by the same practitioners.