Vulnerability & Patch Management Toolkit
Build a vulnerability management program that tracks from discovery to remediation — with the operational workflows your team needs to run it.
Designed by an active security practitioner
3–6 months
Saved vs. building from scratch
$25K–$50K
In labor costs you don't spend
Day 1
Your program is operational
Every day without documented security governance is a day your organization is exposed to audits, questionnaires, and incidents it cannot respond to systematically.
Vulnerability & Patch Management Toolkit
Not ready to buy? Try a sample first.
Download free documents and assessment tools — no email required.
Your scanner finds 200 vulnerabilities. Now what?
Without documented SLAs, nobody knows what “critical” means. Without tracking, vulnerabilities get found and forgotten. Without a policy, there’s no accountability when a 6-month-old critical vulnerability leads to a breach. Auditors, insurers, and customers all expect documented vulnerability management — and “we run Nessus” isn’t a program.
This toolkit gives you the governance layer that turns scan results into action — policies, procedures, SLAs, and tracking workbooks deployable by Friday.
What’s inside
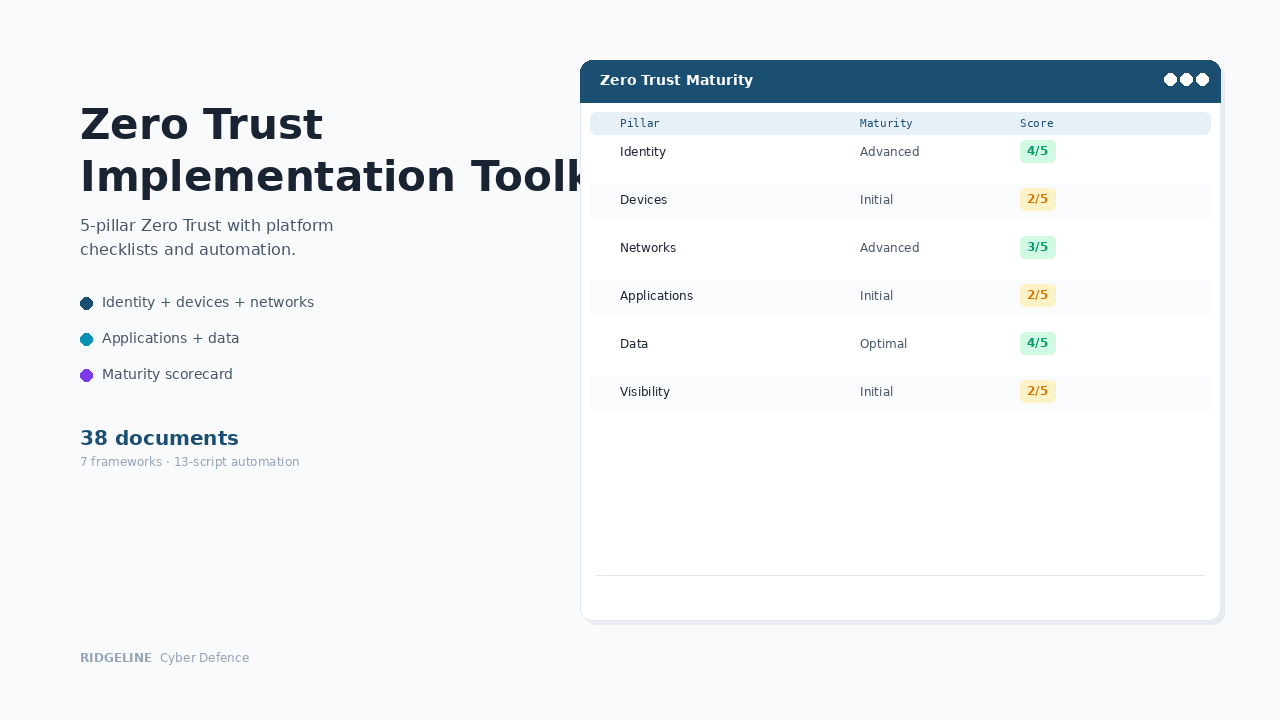
Define the program
The governance documents auditors and insurers ask for first.
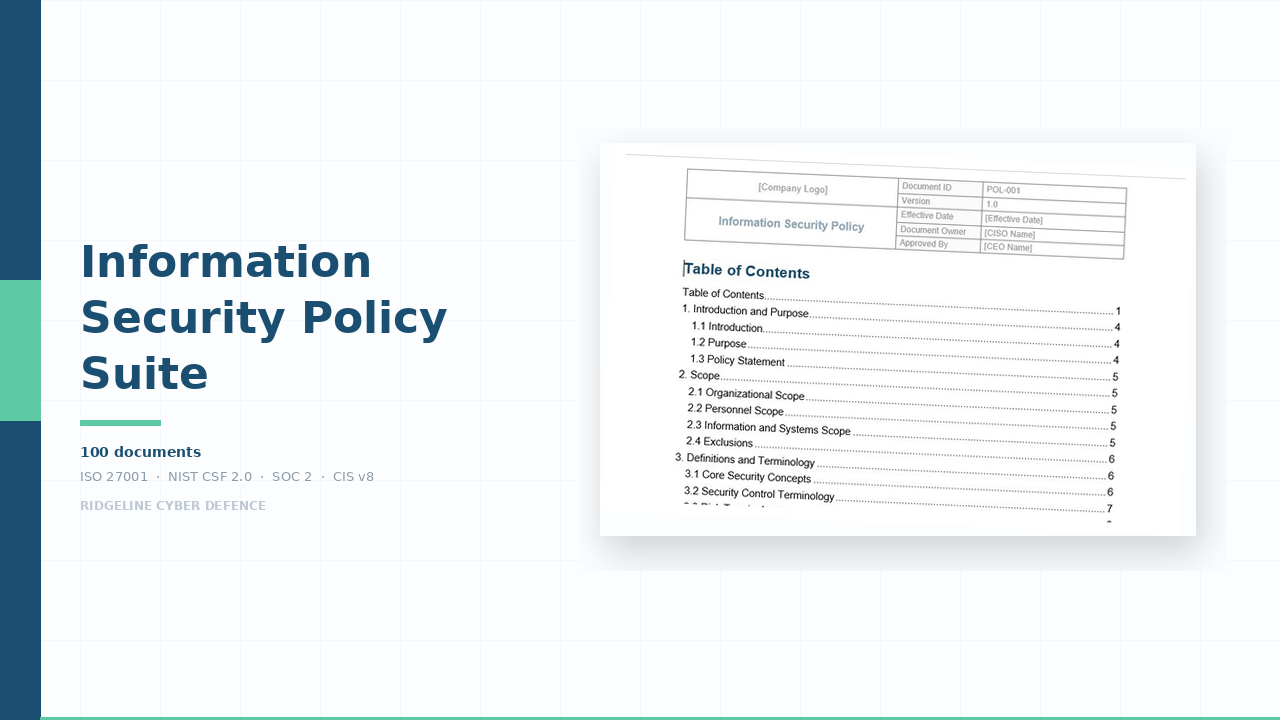
Vulnerability Management Policy
Board-level policy establishing accountability, scope, and governance. Maps to NIST CSF 2.0, ISO 27001:2022, and CIS Controls v8.
The first thing your auditor asks forEndpoint Security Standard
Technical requirements with specific SLAs by severity and asset tier. Critical on Tier 1: 24 hours. High on Tier 2: 7 days. Medium: 30 days. Low: 90 days.
No ambiguity about what "urgent" meansOperate the lifecycle
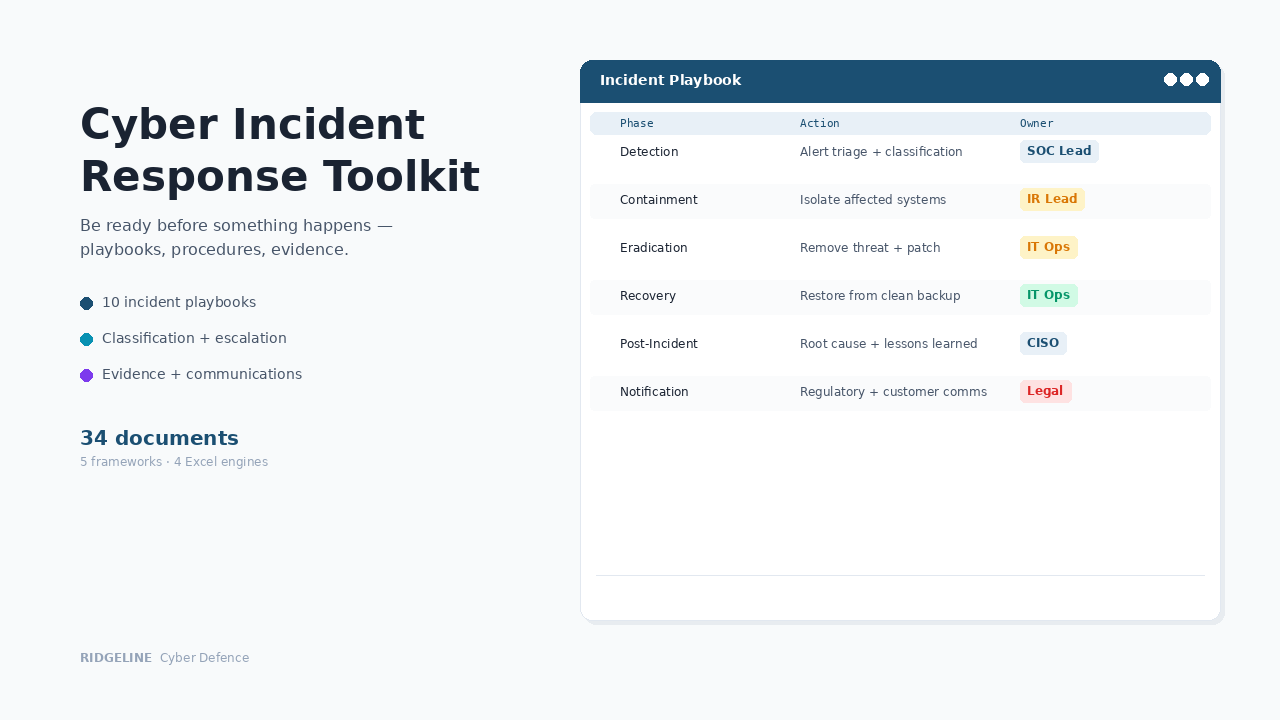
Step-by-step processes and response procedures your team can execute.
Vulnerability Management Procedure
Full lifecycle from identification through verification — numbered steps, responsible parties, timelines, and escalation paths.
Repeatable process that survives staff turnoverVulnerability Scanning Procedure
Operational procedure for running and scheduling scans. Implementation notes scale from startups to enterprises.
Systematic scanning, not reactive scramblingVulnerability Management Playbook
Response playbook for vulnerability discovery, triage, and remediation — decision trees for prioritisation.
Every vulnerability gets the right response at the right speedTrack and prove
Excel workbooks that track remediation and provide audit evidence.
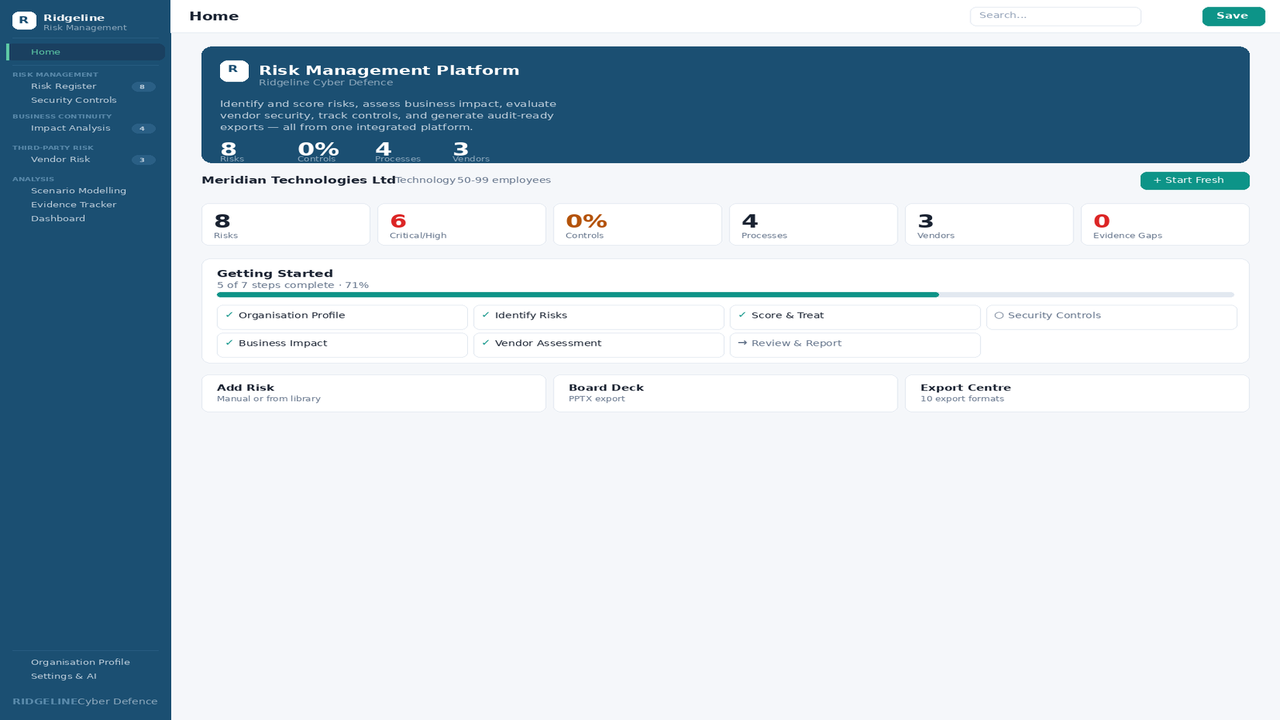
Vulnerability Remediation Tracker
Excel workbook linking vulnerabilities to assets, owners, and timelines. Conditional formatting highlights overdue items automatically.
No more finding the same critical vulnerability scan after scanPatch Management Tracker
Severity ratings, SLA calculations, status tracking, and owner assignment. Built-in dashboard for reporting.
"Show me your patching cadence" — 30 secondsRisk Assessment Workbook
Excel workbook for scoring and prioritising vulnerability-related risks with treatment plans.
Risk-based prioritisation, not CVSS aloneWhat these documents actually look like
Every Excel workbook includes conditional formatting, dropdown menus, automatic SLA calculations, and sample data showing exactly how to use it. Word documents contain complete content with specific parameters — not “insert best practice here” placeholders.
The governance layer that turns scan results into action
Policy · SLAs · Procedures · Playbook · Tracking · Evidence
When someone asks, here’s what happens
Auditor asks for your vulnerability management program
You show them the policy, the severity-based SLAs, the tracking workbooks with remediation timelines, and the scanning procedure. Framework-mapped documentation from day one.
Insurer asks about patch timelines
You pull the Patch Management Tracker — severity-based SLAs, current status, overdue items flagged. A documented, measurable patching program — not guesswork.
Scanner finds a critical vulnerability
The playbook defines triage and response. The SLA says 24 hours on Tier 1 assets. The tracker assigns an owner with a deadline. Conditional formatting flags it if it goes overdue.
The cost comparison
Who this is for
✓ Right fit
Organizations that run vulnerability scanners but lack the governance, tracking, and SLA documentation to turn findings into a measurable program. IT teams responding to audit findings or insurer requirements around patch management.
✗ Not the right fit
Organizations looking for scanning technology — this provides the governance layer, not the scanner itself. Works with any scanner: Nessus, Qualys, Rapid7, OpenVAS, or cloud-native tools. If you need the full policy suite, the Information Security Policy Suite includes VM documentation plus 92 more.
Common questions
Do I need vulnerability scanning tools?
Yes. This toolkit provides the governance, documentation, and tracking — not the scanning technology itself. Works with any scanner: Nessus, Qualys, Rapid7, OpenVAS, or cloud-native tools.
What file formats are included?
Policies and procedures are Word (.docx). Trackers and workbooks are Excel (.xlsx). All files use standard fonts and formatting — compatible with Microsoft 365, Google Workspace, and LibreOffice.
What's the difference between this and the full Information Security Policy Suite?
This toolkit focuses specifically on vulnerability and patch management — 8 targeted documents. The full suite includes all 18 policies plus standards, processes, procedures, and an application. If you only need VM documentation, this is more focused and affordable.
Do I get updates if the product is improved?
Yes. If we update this product within 12 months of your purchase — framework changes, new templates, content improvements — you receive the updated files automatically at no additional cost. After 12 months, you keep everything you have permanently. Future updates are available at a renewal discount.
Is AI used in creating these documents?
Ridgeline uses AI tools in the research and drafting process. All documentation is written, reviewed, and validated by a security practitioner to ensure it is operationally sound and aligned with current frameworks.
What if we need help customising it?
Our Document Customization service will customize the documentation to your environment. Foundation tier from $1,997, Compliance from $3,497. Delivered in 7–10 business days.
How does this compare?
| Capability | Free templates | Vulnerability & Patch Management Toolkit | GRC platform ($15K+/yr) |
|---|---|---|---|
| Framework-aligned documentation | Some | ✓ Full coverage | ✓ |
| Editable Word/Excel files | ✓ | ✓ | ✗ Locked in platform |
| Interactive browser app | ✗ | ✗ | ✓ |
| One-time cost | ✓ Free | ✓ $497 | ✗ Annual subscription |
| Implementation time | Weeks | ✓ Hours | Months |
| Audit-ready formatting | ✗ Inconsistent | ✓ Professional | ✓ |
Get notified about updates to this toolkit
Get notified when we launch new toolkits
Product launches only · No spam · Unsubscribe anytime
Customer Reviews
What buyers are saying about Vulnerability & Patch Management Toolkit
Rate this product
Purchased Vulnerability & Patch Management Toolkit? Your review helps other security professionals make informed decisions.
Document Customization
Need this customized to your organization?
You complete an intake form. We customize every document — industry context, regulatory mapping, calibrated parameters, risk pre-population. Delivered in 7–10 business days.
Foundation $1,997 · Compliance $3,497 · Product purchase separate
Need the skills to operate the program? Our training platform builds the capability — 9 courses at training.ridgelinecyber.com →